Disposable numbers, while useful for privacy protection, can also create harm to consumers and potential risks to enterprises. This is because when free or low-cost disposable numbers are part of the user verification, One-Time-Password (OTP), process fraudsters can use those same numbers to run scam, phishing, impersonation and spam campaigns. For more background, read this earlier GSMA blog in the series: .
GSMA Industry Services recently analysed one week of SMS messages received by free disposable number websites to see which types of enterprises are most affected.
The chart below shows the share of messages by company type:
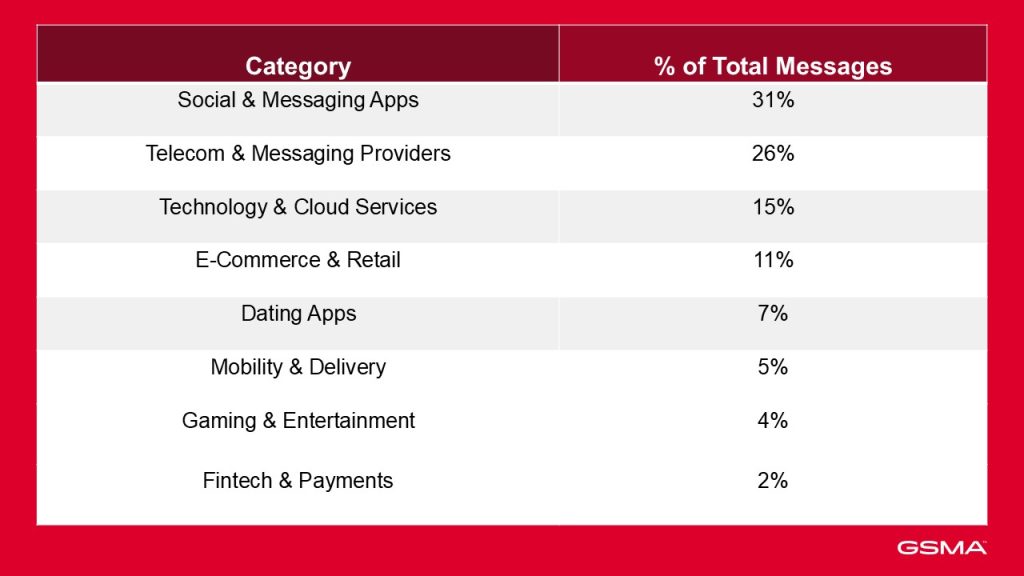
Over the seven days for which traffic was observed, most of the OTPs sent to disposable numbers came from social and messaging apps, followed closely by telecom and messaging providers that deliver SMS traffic to other platforms.
Overall, the data highlights the widespread use of disposable numbers and how it affects well-known brands and their users.
It’s important to know that attackers can complete account verification using free or low‑cost disposable numbers, making it easy for fraudsters to:
- Create large volumes of seemingly legitimate accounts
- Recycle numbers repeatedly to bypass blocking mechanisms
- Run scam, phishing, impersonation or spam campaigns behind accounts that appear “verified”.
Social and messaging apps: trust under pressure
For social and messaging platforms, phone‑verified accounts are intended to provide a basic trust signal: they indicate a human user, reduce bot creation and help limit spam.
When users can falsely verify accounts with free disposable numbers, that signal weakens. Attackers can create and recycle large volumes of accounts that look legitimate but are used for scam, phishing and impersonation.
This has two consequences:
First, and most importantly, it undermines user trust when people receive messages from accounts that appear verified. This is especially damaging for platforms where identity and credibility are central to user interactions.
When malicious actors verify fake accounts using disposable numbers, the verification badge or “phone‑verified” status no longer signals authenticity. Users cannot easily distinguish between genuine people and fake actors operating at scale, which leads to:
- Lower trust in messages received from verified accounts
- Increased susceptibility to scams and impersonation
- Reduced confidence in platform safety overall
Secondly, disposable-number–verified accounts also distort platform analytics:
- They inflate active user and verified user counts
- They introduce large numbers of short‑lived, low‑quality or malicious accounts
- They degrade the reliability of engagement metrics, DAUs (daily active users)/MAUs (monthly active users), and verification rates.
This makes it harder for platforms to understand real user behavior, measure growth or assess the effectiveness of safety systems. It can also mislead advertisers, partners and decision‑makers about true platform health.
Technology and cloud services: free tier abuse
Technology and cloud service providers often use phone verification as an effective control to protect their free tiers, prevent automated sign-ups and limit abuse of resources. These verification steps are used to:
- Confirm that a user is a real person
- Enforce rate limits and quotas
- Restrict free API (Application Programming Interface) keys to one per legitimate user
- Prevent attackers from spinning up unlimited accounts
However, when fraudsters use disposable phone numbers, these protections break down.
Disposable Numbers bypass free-tier safeguards
Cloud providers typically assume that a phone number represents a unique and consistent user. Disposable numbers undermine this assumption as they enable fraudsters to create thousands of accounts using cheap, temporary numbers and automate the process with publicly available SMS-receiving websites, appearing as many different “verified” users, even though they control all the accounts.
Taking unfair advantage of cloud resources, storage, APIs and developer tools
Once attackers bypass onboarding controls, they can exploit free-tier limits by:
- Using disposable numbers to create lots of fake cloud accounts, launch many powerful cloud servers and use those machines to mine cryptocurrency at the cloud provider’s expense.
- Generating large volumes of API requests
- Using multiple free-tier credits across countless fake accounts
- Testing attacks
- Abusing email, SMS or notification services included in free tiers
This results in resource drain, cost spikes and service degradation for legitimate users.
Degrading key security controls
Degrading key security controls means the safety systems that rely on real phone numbers – stable identities, rate limits or device consistency, stop working because attackers can easily fake all those signals using disposable numbers.
Cloud platforms use SMS-based verification to prevent:
- Account farming
- Free credit abuse
- Trial misuse
- Automated API key generation
- Malicious workloads (cracking passwords, mining crypto, sending spam or attacking other systems)
Broader impact on platform health
When attackers use disposable numbers to mass‑create accounts, it leads to:
- Inflated user sign-up metrics
- Higher fraud and abuse incidents
- Increased support and moderation costs
- Wasted infrastructure resources
- Noisy data in activation and retention metrics
- Revenue loss from “never-converting” free-tier abusers
For cloud providers, this becomes a persistent operational and security burden.
Erosion of SMS OTP value for enterprises and the entire ecosystem
Messaging providers serve as the infrastructure layer that delivers one‑time passwords (OTPs) from enterprises—such as banks, government services, e‑commerce platforms, and social apps—to end users. OTPs are meant to provide a trusted authentication channel, ensuring that only legitimate users can complete logins, transactions and account registrations.
However, when a significant share of these OTPs is sent to disposable number websites, the value of SMS as a secure authentication channel deteriorates. Disposable numbers allow attackers to receive OTPs anonymously and at scale, undermining the purpose of the verification process.
How to prevent this erosion and maintain the viability of SMS OTP
GSMA Disposable Number Check is an API-based service that can be implemented in sign-up and re-verification processes, before a one-time password is sent. By instantly identifying disposable numbers, businesses can prevent them from being used to create fraudulent accounts, reducing the risk of account takeover, spam and scams.
Disposable Number Check confers the following benefits:
- It protects users from direct harm caused by scammers who create “verified” accounts to scam, harass or impersonate others.
- It stops disposable numbers from being used to bypass age verification on services intended for adults only, ensuring compliance and protecting vulnerable users.
- It helps stop attempts to bypass geographical restrictions in the provision of services, especially fintech and crypto.
- It prevents the repeated abuse of promotions, free trials and discounts, which are common targets for fraudsters seeking to exploit systems at scale.
The service is one small change with a significant impact. If you’re interested in finding out more or want to book a demo, please fill out the form below.